When Types of Cyber Attacks came to importance, security was once a rarity, but today it’s always a must-have. This blog will assist you in being knowledgeable about the common Cyber Attacks of today.
The topic of cyber security is rapidly developing, and as a result, there are many available positions for qualified candidates. This Cyber Security Course is perfect for you if you’re thinking about a future in the field of computer network defense and assault. Or if you’d prefer not to work in this field but get experts to help you make things as secure as possible, it’s worth exploring the options when it comes to comprehensive SIEM management.
Here are 10 Types of Cyber Attacks You Should Be Aware in 2025;
1. Malware
Malicious software, often known as malware, is introduced into systems and networks to wreak havoc on the computers, servers, workstations, and networks involved It can infiltrate computer networks, steal private information, and block access to services. IT departments use firewalls and security software to prevent malware from entering networks and systems, but malware is constantly evolving to evade detection and prevention. Because of the Types of Cyber Attacks, it’s vital to always use the most recent versions of firewalls and other forms of security software.
2. Stealth Virus
Some viruses can remain hidden because they modify certain aspects of the system. They can do this by compromising detection programs. These may also be spread by malicious software, infected attachments, or unauthorized website installs.
3. The Third Threat Is Drive-By Shootings
Hackers use drive-by attacks to inject harmful code into weak websites. The script is automatically executed on the page, infecting a user’s PC with the virus when they see it. The term “drive-by infection” refers to the fact that a person may get infected simply by visiting a site and “driving by” an infected page. You are under no obligation to provide any personal details or interact with the site in any way.
4. Phishing
Phishing is a kind of social engineering, yet it’s important enough to discuss on its own, much as ransomware is. Like smishing (through SMS) and vishing (via a video message), these assaults try to deceive victims into giving over sensitive information (phone). Criminals may use phishing to persuade victims to reveal important information by tricking them into clicking on malicious links or downloading infected files. Malicious code often propagates after it has been introduced Types of Cyber Attacks.
To safeguard against such dangers, educate your workers on how to thoroughly evaluate each link, file, or download they receive. The integrity of any company’s data might be jeopardized by an email that seems harmless at first glance. Since legitimate and phishing emails often share visual design cues, it’s not always easy to tell them apart.
5. Trojan horse
In a Trojan horse attack, malicious software is concealed behind a safe website or mobile app.
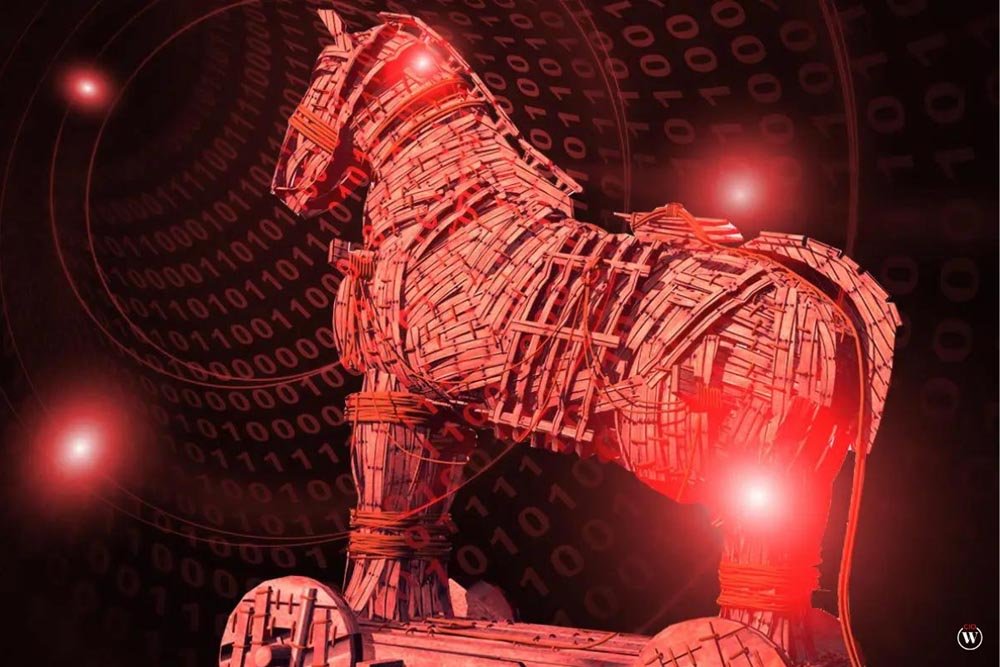
When a user launches the Trojan, which seems to be a benign program, the malware within may create a backdoor into the system, enabling hackers to access the computer or network. The term for this danger comes from the myth of the Greek soldiers who rode into Troy concealed behind a wooden horse and ultimately won the battle.
6. Cryptojacking
Cryptojacking is when hackers exploit other people’s devices (PCs, mobile phones, tablets, and even servers) to mine cryptocurrency without their knowledge or consent in Types of Cyber Attacks.
Like many forms of cybercrime, the motivation behind this threat is financial. This assault, in contrast to others like it, is meant to go undetected by the victim. Hackers make money by covertly accessing other people’s computers to mine cryptocurrencies, which requires a lot of computing power.
7. Ransomware
To prevent you from accessing your computer and the information stored on it, ransomware encrypts your files and then demands a ransom to be paid in exchange for unlocking them. The computer can freeze, encrypt or delete data, or become inaccessible altogether. If the victim pays the attacker a ransom, the attacker will unlock the data for them Types of Cyber Attacks.
8. Brute-Force-Attack
One definition of “brute-force attack” is an assault that makes use of no strategy beyond sheer force. The attacker attempts to figure out the login credentials of a user with access to the target system through osmosis. As soon as they understand it well, they are let in.
Cybercriminals commonly use bots to break passwords, even though doing so is a laborious and tough task.
The attacker patiently waits as the bot checks each subsequent option. After submitting his credentials, the thief is let in. After submitting his credentials, the thief is let inside Types of Cyber Attacks.
9. Spyware
These tools are designed to spy on people, their computers, and their online activities. Your every motion is tracked and sent to the hacker invisibly (s). When you download free software, they often come along for the ride.

10. Eavesdropping Attacks
Eavesdropping attacks include a third party intercepting data as it travels via a network. This is a tactic an attacker might employ to steal sensitive information, such as login credentials or credit card details. It’s possible to eavesdrop either proactively or passively.
A hacker engages in active eavesdropping when he or she inserts software into the data stream of a network to collect information. Passive eavesdropping attacks are unique because the hacker literally “listens in,” or eavesdrops on the communications, in quest of useful information in Types of Cyber Attacks.
But to help prevent this, businesses and individuals are increasingly turning to encrypted communication, which protects data by scrambling it during transmission. Even if someone intercepts the message, it’s unreadable without the decryption key, making it a smart and essential layer of defense. Honestly, it’s the best decision